Data Communication And Networking In Hindi Pdf
By: Abijeet Singh BhadauriaJagran Institute Of ManagementBasic Networking Concepts 1. 4.Introduction Protocols Protocol Layers Network Interconnection/Internet11.
Introduction-A network can be defined as a group of computers and other devices connected in some ways so as to be able to exchange data.Each of the devices on the network can be thought of as a node; each node has a unique address.Addresses are numeric quantities that are easy for computers to work with, but not for humans to remember. Example: 204.160.241.98 -Some networks also provide names that humans can more easily remember than numbers. Example: www.javasoft.com, corresponding to the above numeric address.
.A computer network is a which allows to share resources. In computer networks, with each other using connections between nodes. These data links are established over such as copper wires or s, and such as.Network computer devices that originate, and terminate the data are called network nodes. Nodes are generally identified by, and can include such as, and, as well as such as routers and switches. Two such devices can be said to be networked together when one device is able to exchange information with the other device, whether or not they have a direct connection to each other. In most cases, application-specific communications are (i.e. Carried as ) over other more general communications protocols.
This formidable collection of requires skilled to keep it all.Computer networks support an enormous number of and such as access to the, shared use of, printers, and, and use of and applications as well as many others. Computer networks differ in the used to carry their signals, to organize network traffic, the network's size, mechanism and organizational intent. The best-known computer network is the.
See also:The chronology of significant computer-network developments includes:. In the late 1950s, early networks of computers included the U.S. Military radar system (SAGE). In 1959, proposed to the Central Committee of the Communist Party of the Soviet Union a detailed plan for the re-organisation of the control of the Soviet armed forces and of the Soviet economy on the basis of a network of computing centres, the. In 1959, the (MOS transistor) was invented by and at. It later became the basic building block of computer network such as, modules, and.
In 1960, the commercial airline reservation system (SABRE) went online with two connected. In 1963, sent a memorandum to office colleagues discussing the concept of the ', a computer network intended to allow general communications among computer users. In 1964, researchers at developed the for distributed users of large computer systems. The same year, at, a research group supported by and used a computer to route and manage telephone connections.
Data Communication And Networking In Hindi Pdf
Throughout the 1960s, and independently developed the concept of to transfer information between computers over a network. Davies pioneered the implementation of the concept with the, a local area network at the using a line speed of 768 kbit/s. In 1965, introduced the first widely used that implemented true computer control. In 1966, Thomas Marill and published a paper on an experimental (WAN) for computer time sharing. In 1969, the first four nodes of the were connected using 50 kbit/s circuits between the, the, the, and the. Carried out theoretical work to model the performance of packet-switched networks, which underpinned the development of the ARPANET.
His theoretical work on in the late 1970s with student remains critical to the operation of the today. In 1972, commercial services using were deployed, and later used as an underlying infrastructure for expanding networks. In 1973, the French network was the first to make the responsible for the reliable delivery of data, rather than this being a centralized service of the network itself. In 1973, wrote a formal memo at describing, a networking system that was based on the, developed in the 1960s by and colleagues at the. In July 1976, and published their paper 'Ethernet: Distributed Packet Switching for Local Computer Networks' and collaborated on several patents received in 1977 and 1978.
In 1974, the first (Transmission Control Protocol) specification, ( Specification of Internet Transmission Control Program), was written by, and Carl Sunshine. Main article:Computer communication links that do not support packets, such as traditional, simply transmit data as a. However, the overwhelming majority of computer networks carry their data in packets. A network packet is a formatted unit of (a list of bits or bytes, usually a few tens of bytes to a few kilobytes long) carried by a. Packets are sent through the network to their destination. Once the packets arrive they are reassembled into their original message.Packets consist of two kinds of data: control information, and user data (payload). The control information provides data the network needs to deliver the user data, for example: source and destination, codes, and sequencing information.
Typically, control information is found in and, with in between.With packets, the of the transmission medium can be better shared among users than if the network were. When one user is not sending packets, the link can be filled with packets from other users, and so the cost can be shared, with relatively little interference, provided the link isn't overused. Often the route a packet needs to take through a network is not immediately available. In that case the packet is and waits until a link is free.Network topology. Main article:The physical layout of a network is usually less important than the topology that connects network nodes.
Most diagrams that describe a physical network are therefore topological, rather than geographic. The symbols on these diagrams usually denote network links and network nodes.Network topology is the layout or organizational hierarchy of interconnected nodes of a computer network. Different network topologies can affect throughput, but reliability is often more critical. With many technologies, such as bus networks, a single failure can cause the network to fail entirely. In general the more interconnections there are, the more robust the network is; but the more expensive it is to install.Common layouts are:.
A: all nodes are connected to a common medium along this medium. This was the layout used in the original, called. This is still a common topology on the, although modern variants use links instead. A: all nodes are connected to a special central node. This is the typical layout found in a, where each wireless client connects to the central.
A: each node is connected to its left and right neighbour node, such that all nodes are connected and that each node can reach each other node by traversing nodes left- or rightwards. The (FDDI) made use of such a topology. A: each node is connected to an arbitrary number of neighbours in such a way that there is at least one traversal from any node to any other.
A: each node is connected to every other node in the network. A: nodes are arranged hierarchically.The physical layout of the nodes in a network may not necessarily reflect the network topology. As an example, with, the network topology is a ring (actually two counter-rotating rings), but the physical topology is often a star, because all neighboring connections can be routed via a central physical location. Physical layout is not completely irrelevant, however, as common ducting and equipment locations can represent single points of failure due to issues like fires, power failures and flooding.Overlay network. A sample overlay networkAn is a virtual computer network that is built on top of another network. Nodes in the overlay network are connected by virtual or logical links. Each link corresponds to a path, perhaps through many physical links, in the underlying network.
The topology of the overlay network may (and often does) differ from that of the underlying one. For example, many networks are overlay networks.
They are organized as nodes of a virtual system of links that run on top of the Internet.Overlay networks have been around since the invention of networking when computer systems were connected over telephone lines using, before any existed.The most striking example of an overlay network is the Internet itself. The Internet itself was initially built as an overlay on the. Even today, each Internet node can communicate with virtually any other through an underlying mesh of sub-networks of wildly different topologies and technologies. And are the means that allow mapping of a fully connected IP overlay network to its underlying network.Another example of an overlay network is a, which maps keys to nodes in the network. In this case, the underlying network is an IP network, and the overlay network is a table (actually a ) indexed by keys.Overlay networks have also been proposed as a way to improve Internet routing, such as through guarantees to achieve higher-quality.
Previous proposals such as, and have not seen wide acceptance largely because they require modification of all in the network. On the other hand, an overlay network can be incrementally deployed on end-hosts running the overlay protocol software, without cooperation from. The overlay network has no control over how packets are routed in the underlying network between two overlay nodes, but it can control, for example, the sequence of overlay nodes that a message traverses before it reaches its destination.For example, manages an overlay network that provides reliable, efficient content delivery (a kind of ). Academic research includes end system multicast, resilient routing and quality of service studies, among others.Network links.
Further information:The transmission media (often referred to in the literature as the ) used to link devices to form a computer network include,. In the, these are defined at layers 1 and 2 — the physical layer and the data link layer.A widely adopted family of transmission media used in (LAN) technology is collectively known as. The media and protocol standards that enable communication between networked devices over Ethernet are defined. Ethernet transmits data over both copper and fiber cables. Standards use radio waves, others use signals as a transmission medium.
Uses a building's to transmit data.Wired technologies. Are used to transmit light from one computer/network node to anotherThe following classes of wired technologies are used in computer networking. is widely used for cable television systems, office buildings, and other work-sites for local area networks. Transmission speed ranges from 200 million bits per second to more than 500 million bits per second. technology uses existing (, phone lines and ) to create a high-speed local area network. cabling is used for wired and other standards.
It typically consists of 4 pairs of copper cabling that can be utilized for both voice and data transmission. The use of two wires twisted together helps to reduce. The transmission speed ranges from 2 Mbit/s to 10 Gbit/s. Twisted pair cabling comes in two forms: unshielded twisted pair (UTP) and shielded twisted-pair (STP).
Each form comes in several, designed for use in various scenarios. 2007 map showing submarine optical fiber telecommunication cables around the world. An is a glass fiber. It carries pulses of light that represent data via lasers. Some advantages of optical fibers over metal wires are very low transmission loss and immunity to electrical interference. Using dense, optical fibers can simultaneously carry multiple streams of data on different wavelengths of light, which greatly increases the rate that data can be sent to up to trillions of bits per second. Optic fibers can be used for long runs of cable carrying very high data rates, and are used for to interconnect continents.
There are two basic types of fiber optics, (SMF) and (MMF). Single-mode fiber has the advantage of being able to sustain a coherent signal for dozens or even a hundred kilometers. Multimode fiber is cheaper to terminate but is limited to a few hundred or even only a few dozens of meters, depending on the data rate and cable grade.Wireless technologies. Main article:Network connections can be established wirelessly using radio or other electromagnetic means of communication. Terrestrial – Terrestrial microwave communication uses Earth-based transmitters and receivers resembling satellite dishes. Terrestrial microwaves are in the low gigahertz range, which limits all communications to line-of-sight.
Relay stations are spaced approximately 40 miles (64 km) apart. – Satellites communicate also communicate via microwave. The satellites are stationed in space, typically in geosynchronous orbit 35,400 km (22,000 mi) above the equator. These Earth-orbiting systems are capable of receiving and relaying voice, data, and TV signals.
use several radio communications technologies. The systems divide the region covered into multiple geographic areas. Each area is served by a low-power. Radio and technologies – use a high-frequency radio technology similar to digital cellular. Wireless LANs use spread spectrum technology to enable communication between multiple devices in a limited area. Defines a common flavor of open-standards wireless radio-wave technology known as. uses visible or invisible light for communications.
In most cases, is used, which limits the physical positioning of communicating devices.Exotic technologies There have been various attempts at transporting data over exotic media:. was a humorous April fool's, issued as. It was implemented in real life in 2001.
Extending the Internet to interplanetary dimensions via radio waves, the.Both cases have a large, which gives slow two-way communication, but doesn't prevent sending large amounts of information.Network nodes. An network interface in the form of an accessory card. A lot of network interfaces are built-in.A (NIC) is that provides a computer with the ability to access the transmission media, and has the ability to process low-level network information. For example, the NIC may have a connector for accepting a cable, or an aerial for wireless transmission and reception, and the associated circuitry.The NIC responds to traffic addressed to a for either the NIC or the computer as a whole.In networks, each network interface controller has a unique (MAC) address—usually stored in the controller's permanent memory. To avoid address conflicts between network devices, the (IEEE) maintains and administers MAC address uniqueness. The size of an Ethernet MAC address is six. The three most significant octets are reserved to identify NIC manufacturers.
These manufacturers, using only their assigned prefixes, uniquely assign the three least-significant octets of every Ethernet interface they produce.Repeaters and hubs A is an device that receives a network, cleans it of unnecessary noise and regenerates it. The signal is at a higher power level, or to the other side of an obstruction, so that the signal can cover longer distances without degradation. In most twisted pair Ethernet configurations, repeaters are required for cable that runs longer than 100 meters.
With fiber optics, repeaters can be tens or even hundreds of kilometers apart.A repeater with multiple ports is known as an. Repeaters work on the physical layer of the OSI model. Repeaters require a small amount of time to regenerate the signal. This can cause a that affects network performance and may affect proper function. As a result, many network architectures limit the number of repeaters that can be used in a row, e.g., the Ethernet.Hubs and repeaters in LANs have been mostly obsoleted by modern.Bridges A connects and filters traffic between two at the (layer 2) of the to form a single network. This breaks the network's collision domain but maintains a unified broadcast domain. Network segmentation breaks down a large, congested network into an aggregation of smaller, more efficient networks.Bridges come in three basic types:.
Local bridges: Directly connect LANs. Remote bridges: Can be used to create a wide area network (WAN) link between LANs. Remote bridges, where the connecting link is slower than the end networks, largely have been replaced with routers.
Wireless bridges: Can be used to join LANs or connect remote devices to LANs.Switches A is a device that forwards and filters between based on the destination MAC address in each frame.A switch is distinct from a hub in that it only forwards the frames to the physical ports involved in the communication rather than all ports connected. It can be thought of as a multi-port bridge.
It learns to associate physical ports to MAC addresses by examining the source addresses of received frames. If an unknown destination is targeted, the switch broadcasts to all ports but the source. Switches normally have numerous ports, facilitating a star topology for devices, and cascading additional switches.Routers. A typical home or small office router showing the telephone line and network cable connectionsA is an device that forwards between networks by processing the routing information included in the packet or datagram (Internet protocol information from layer 3). The routing information is often processed in conjunction with the routing table (or forwarding table). A router uses its routing table to determine where to forward packets. A destination in a routing table can include a 'null' interface, also known as the 'black hole' interface because data can go into it, however, no further processing is done for said data, i.e.
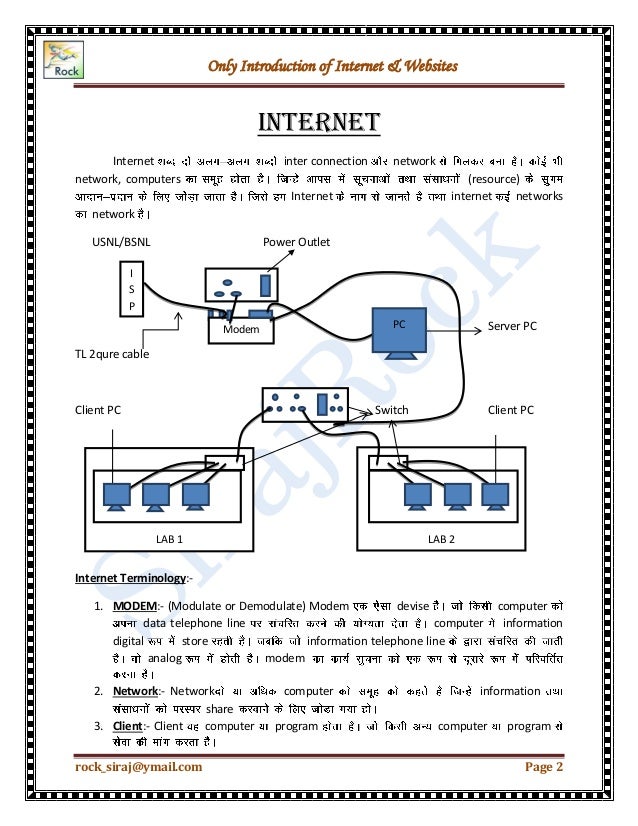
The packets are dropped.Modems (MOdulator-DEModulator) are used to connect network nodes via wire not originally designed for digital network traffic, or for wireless. To do this one or more are by the digital signal to produce an that can be tailored to give the required properties for transmission. Modems are commonly used for telephone lines, using a technology.Firewalls A is a network device for controlling network security and access rules. Firewalls are typically configured to reject access requests from unrecognized sources while allowing actions from recognized ones. The vital role firewalls play in network security grows in parallel with the constant increase in.Communication protocols. Message flows (A-B) in the presence of a router (R), red flows are effective communication paths, black paths are across the actual network links.A is a set of rules for exchanging information over a network. In a (also see the ), each protocol leverages the services of the protocol layer below it, until the lowest layer controls the hardware which sends information across the media.
The use of protocol layering is today ubiquitous across the field of computer networking. An important example of a protocol stack is (the World Wide Web protocol) running over over (the ) over (the Wi-Fi protocol). This stack is used between the and the home user's personal computer when the user is surfing the web.Communication protocols have various characteristics. They may be or, they may use or, and they may use hierarchical addressing or flat addressing.There are many communication protocols, a few of which are described below.IEEE 802 is a family of IEEE standards dealing with local area networks and metropolitan area networks. The complete IEEE 802 protocol suite provides a diverse set of networking capabilities. The protocols have a flat addressing scheme. They operate mostly at levels 1 and 2 of the.For exampledeals with the routing of Ethernet packets using a.
Describes, and defines a port-based protocol, which forms the basis for the authentication mechanisms used in VLANs (but it is also found in WLANs) – it is what the home user sees when the user has to enter a 'wireless access key'.Ethernet , sometimes simply called LAN, is a family of protocols used in wired LANs, described by a set of standards together called published by the.Wireless LAN , also widely known as WLAN or WiFi, is probably the most well-known member of the protocol family for home users today. It is standardized by and shares many properties with wired Ethernet.Internet Protocol Suite The, also called TCP/IP, is the foundation of all modern networking. It offers connection-less as well as connection-oriented services over an inherently unreliable network traversed by data-gram transmission at the (IP) level. At its core, the protocol suite defines the addressing, identification, and routing specifications for (IPv4) and for IPv6, the next generation of the protocol with a much enlarged addressing capability.SONET/SDH (SONET) and Synchronous Digital Hierarchy (SDH) are standardized protocols that transfer multiple digital bit streams over optical fiber using lasers.
They were originally designed to transport circuit mode communications from a variety of different sources, primarily to support real-time, uncompressed, voice encoded in (Pulse-Code Modulation) format. However, due to its protocol neutrality and transport-oriented features, SONET/SDH also was the obvious choice for transporting (ATM) frames.Asynchronous Transfer Mode (ATM) is a switching technique for telecommunication networks. It uses asynchronous and encodes data into small, fixed-sized. This differs from other protocols such as the or that use variable sized packets. ATM has similarity with both and switched networking. This makes it a good choice for a network that must handle both traditional high-throughput data traffic, and real-time, content such as voice and video. ATM uses a model in which a must be established between two endpoints before the actual data exchange begins.While the role of ATM is diminishing in favor of, it still plays a role in the, which is the connection between an and the home user.
Cellular standards There are a number of different digital cellular standards, including: (GSM), (GPRS), (EV-DO), (EDGE), (UMTS), (DECT), (IS-136/TDMA), and (iDEN). Geographic scale typesby spatial scope.A network can be characterized by its physical capacity or its organizational purpose.
Use of the network, including user authorization and access rights, differ accordingly.Nanoscale networkA network has key components implemented at the nanoscale including message carriers and leverages physical principles that differ from macroscale communication mechanisms. Nanoscale communication extends communication to very small sensors and actuators such as those found in biological systems and also tends to operate in environments that would be too harsh for classical communication. Personal area networkA (PAN) is a computer network used for communication among computer and different information technological devices close to one person. Some examples of devices that are used in a PAN are personal computers, printers, fax machines, telephones, PDAs, scanners, and even video game consoles. A PAN may include wired and wireless devices.

The reach of a PAN typically extends to 10 meters. A wired PAN is usually constructed with USB and FireWire connections while technologies such as Bluetooth and infrared communication typically form a wireless PAN.Local area networkA (LAN) is a network that connects computers and devices in a limited geographical area such as a home, school, office building, or closely positioned group of buildings. Each computer or device on the network is a.
Wired LANs are most likely based on technology. Newer standards such as also provide a way to create a wired LAN using existing wiring, such as coaxial cables, telephone lines, and power lines.The defining characteristics of a LAN, in contrast to a (WAN), include higher, limited geographic range, and lack of reliance on to provide connectivity. Current Ethernet or other LAN technologies operate at data transfer rates up to, standardized by in 2010. Currently, is being developed.A LAN can be connected to a WAN using a.Home area networkA (HAN) is a residential LAN used for communication between digital devices typically deployed in the home, usually a small number of personal computers and accessories, such as printers and mobile computing devices. An important function is the sharing of Internet access, often a broadband service through a cable TV or (DSL) provider.Storage area networkA (SAN) is a dedicated network that provides access to consolidated, block level data storage. SANs are primarily used to make storage devices, such as disk arrays, tape libraries, and optical jukeboxes, accessible to servers so that the devices appear like locally attached devices to the operating system. A SAN typically has its own network of storage devices that are generally not accessible through the local area network by other devices.
The cost and complexity of SANs dropped in the early 2000s to levels allowing wider adoption across both enterprise and small to medium-sized business environments.Campus area networkA (CAN) is made up of an interconnection of LANs within a limited geographical area. The networking equipment (switches, routers) and transmission media (optical fiber, copper plant, cabling, etc.) are almost entirely owned by the campus tenant / owner (an enterprise, university, government, etc.).For example, a university campus network is likely to link a variety of campus buildings to connect academic colleges or departments, the library, and student residence halls.Backbone networkA is part of a computer network infrastructure that provides a path for the exchange of information between different LANs or sub-networks. A backbone can tie together diverse networks within the same building, across different buildings, or over a wide area.For example, a large company might implement a backbone network to connect departments that are located around the world. The equipment that ties together the departmental networks constitutes the network backbone. When designing a network backbone, and are critical factors to take into account. Normally, the backbone network's capacity is greater than that of the individual networks connected to it.Another example of a backbone network is the, which is a massive, global system of fiber-optic cable and optical networking that carry the bulk of data between (WANs), metro, regional, national and transoceanic networks.Metropolitan area networkA (MAN) is a large computer network that usually spans a city or a large campus.Wide area networkA (WAN) is a computer network that covers a large geographic area such as a city, country, or spans even intercontinental distances. A WAN uses a communications channel that combines many types of media such as telephone lines, cables, and air waves.
A WAN often makes use of transmission facilities provided by common carriers, such as telephone companies. WAN technologies generally function at the lower three layers of the: the, the, and the.Enterprise private networkAn is a network that a single organization builds to interconnect its office locations (e.g., production sites, head offices, remote offices, shops) so they can share computer resources.Virtual private networkA (VPN) is an overlay network in which some of the links between nodes are carried by open connections or virtual circuits in some larger network (e.g., the Internet) instead of by physical wires. The data link layer protocols of the virtual network are said to be tunneled through the larger network when this is the case.
One common application is secure communications through the public Internet, but a VPN need not have explicit security features, such as authentication or content encryption. VPNs, for example, can be used to separate the traffic of different user communities over an underlying network with strong security features.VPN may have best-effort performance, or may have a defined service level agreement (SLA) between the VPN customer and the VPN service provider. Generally, a VPN has a topology more complex than point-to-point.Global area networkA (GAN) is a network used for supporting mobile across an arbitrary number of wireless LANs, satellite coverage areas, etc.
The key challenge in mobile communications is handing off user communications from one local coverage area to the next. In IEEE Project 802, this involves a succession of terrestrial. Organizational scope Networks are typically managed by the organizations that own them. Private enterprise networks may use a combination of intranets and extranets. They may also provide network access to the, which has no single owner and permits virtually unlimited global connectivity.Intranet An is a set of networks that are under the control of a single administrative entity. The intranet uses the protocol and IP-based tools such as web browsers and file transfer applications. The administrative entity limits use of the intranet to its authorized users.
Most commonly, an intranet is the internal LAN of an organization. A large intranet typically has at least one web server to provide users with organizational information. An intranet is also anything behind the router on a local area network.Extranet An is a network that is also under the administrative control of a single organization, but supports a limited connection to a specific external network.
For example, an organization may provide access to some aspects of its intranet to share data with its business partners or customers. These other entities are not necessarily trusted from a security standpoint. Network connection to an extranet is often, but not always, implemented via WAN technology.Internetwork An is the connection of multiple computer networks via a common routing technology using routers.Internet. Partial map of the Internet based on the January 15, 2005 data found on. Each line is drawn between two nodes, representing two.
The length of the lines are indicative of the delay between those two nodes. This graph represents less than 30% of the networks reachable.The is the largest example of an internetwork.
It is a global system of interconnected governmental, academic, corporate, public, and private computer networks. It is based on the networking technologies of the. It is the successor of the (ARPANET) developed by of the. The Internet utilizes copper communications and the backbone to enable the (WWW), the, video transfer and a broad range of information services.Participants in the Internet use a diverse array of methods of several hundred documented, and often standardized, protocols compatible with the Internet Protocol Suite and an addressing system administered by the. Service providers and large enterprises exchange information about the of their address spaces through the (BGP), forming a redundant worldwide mesh of transmission paths.Darknet A is an overlay network, typically running on the Internet, that is only accessible through specialized software. A darknet is an anonymizing network where connections are made only between trusted peers — sometimes called 'friends' — using non-standard and.Darknets are distinct from other distributed networks as is anonymous (that is, are not publicly shared), and therefore users can communicate with little fear of governmental or corporate interference.
Routing calculates good paths through a network for information to take. For example, from node 1 to node 6 the best routes are likely to be 1-8-7-6 or 1-8-10-6, as this has the thickest routes.is the process of selecting network paths to carry network traffic. Routing is performed for many kinds of networks, including networks and.In packet switched networks, routing directs (the transit of logically addressed from their source toward their ultimate destination) through intermediate. Intermediate nodes are typically network hardware devices such as,. General-purpose can also forward packets and perform routing, though they are not specialized hardware and may suffer from limited performance.
The routing process usually directs forwarding on the basis of, which maintain a record of the routes to various network destinations. Main article: Network security consists of provisions and policies adopted by the to prevent and monitor access, misuse, modification, or denial of the computer network and its network-accessible resources. Network security is the authorization of access to data in a network, which is controlled by the network administrator. Users are assigned an ID and password that allows them access to information and programs within their authority. Network security is used on a variety of computer networks, both public and private, to secure daily transactions and communications among businesses, government agencies and individuals.Network surveillance is the monitoring of data being transferred over computer networks such as the. The monitoring is often done surreptitiously and may be done by or at the behest of governments, by corporations, criminal organizations, or individuals.
It may or may not be legal and may or may not require authorization from a court or other independent agency.Computer and network surveillance programs are widespread today, and almost all Internet traffic is or could potentially be monitored for clues to illegal activity.Surveillance is very useful to governments and to maintain, recognize and monitor threats, and prevent/investigate activity. With the advent of programs such as the program, technologies such as and software, and laws such as the, governments now possess an unprecedented ability to monitor the activities of citizens.However, many and groups—such as, the, and the —have expressed concern that increasing surveillance of citizens may lead to a society, with limited political and personal freedoms. Fears such as this have led to numerous lawsuits such as. The group has hacked into government websites in protest of what it considers 'draconian surveillance'. End to end encryption (E2EE) is a paradigm of uninterrupted protection of data traveling between two communicating parties.
It involves the originating party data so only the intended recipient can decrypt it, with no dependency on third parties. End-to-end encryption prevents intermediaries, such as or, from discovering or tampering with communications.
End-to-end encryption generally protects both and.Examples of end-to-end encryption include for web traffic, for, for, for, and for radio.Typical -based communications systems do not include end-to-end encryption. These systems can only guarantee protection of communications between and, not between the communicating parties themselves. Examples of non-E2EE systems are,. Some such systems, for example LavaBit and SecretInk, have even described themselves as offering 'end-to-end' encryption when they do not. Some systems that normally offer end-to-end encryption have turned out to contain a that subverts negotiation of the between the communicating parties, for example or.The end-to-end encryption paradigm does not directly address risks at the communications endpoints themselves, such as the of, poor quality,.
E2EE also does not address, which relates to things such as the identities of the end points and the times and quantities of messages that are sent.SSL/TLS The introduction and rapid growth of e-commerce on the World Wide Web in the mid-1990s made it obvious that some form of authentication and encryption was needed. Took the first shot at a new standard. At the time, the dominant web browser was. Netscape created a standard called secure socket layer (SSL). SSL requires a server with a certificate. When a client requests access to an SSL-secured server, the server sends a copy of the certificate to the client. The SSL client checks this certificate (all web browsers come with an exhaustive list of CA root certificates preloaded), and if the certificate checks out, the server is authenticated and the client negotiates a symmetric-key cipher for use in the session.

The session is now in a very secure encrypted tunnel between the SSL server and the SSL client. Views of networks Users and network administrators typically have different views of their networks. Users can share printers and some servers from a workgroup, which usually means they are in the same geographic location and are on the same LAN, whereas a Network Administrator is responsible to keep that network up and running.
A has less of a connection of being in a local area, and should be thought of as a set of arbitrarily located users who share a set of servers, and possibly also communicate via technologies.Network administrators can see networks from both physical and logical perspectives. The physical perspective involves geographic locations, physical cabling, and the network elements (e.g., and ) that interconnect via the transmission media. Logical networks, called, in the TCP/IP architecture, map onto one or more transmission media.
For example, a common practice in a campus of buildings is to make a set of LAN cables in each building appear to be a common subnet, using technology.Both users and administrators are aware, to varying extents, of the trust and scope characteristics of a network. Again using TCP/IP architectural terminology, an is a community of interest under private administration usually by an enterprise, and is only accessible by authorized users (e.g.
Intranets do not have to be connected to the Internet, but generally have a limited connection. An is an extension of an intranet that allows secure communications to users outside of the intranet (e.g. Business partners, customers).Unofficially, the Internet is the set of users, enterprises, and content providers that are interconnected by (ISP). From an engineering viewpoint, the is the set of subnets, and aggregates of subnets, which share the registered space and exchange information about the reachability of those IP addresses using the. Typically, the names of servers are translated to IP addresses, transparently to users, via the directory function of the (DNS).Over the Internet, there can be, and communications. When money or sensitive information is exchanged, the communications are apt to be protected by some form of mechanism. Intranets and extranets can be securely superimposed onto the Internet, without any access by general Internet users and administrators, using secure (VPN) technology.Journals and newsletters.
( journal)See also.References.
Comments are closed.
